Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
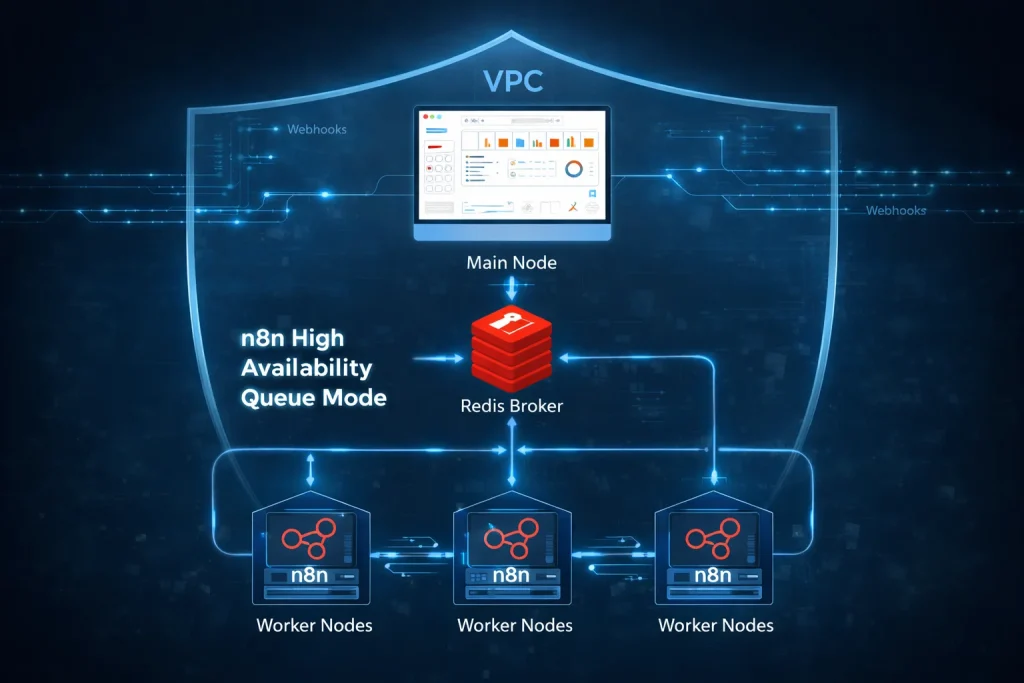
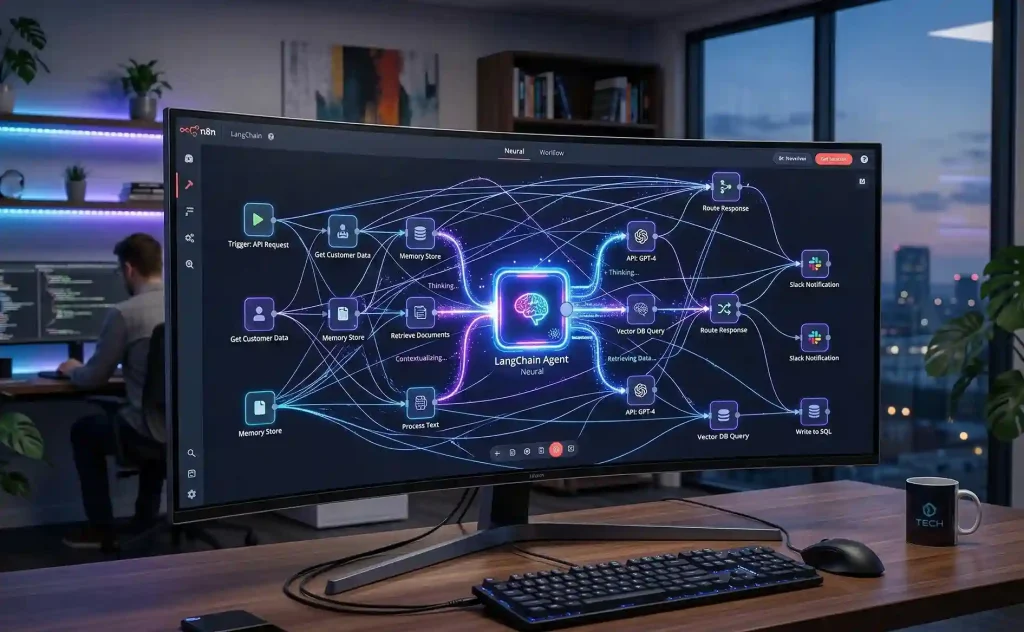
Don’t Let Workflows Crash: The n8n Performance Guide for Power Users
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
The Error-Free Office: Advanced Error Handling, Paths, and Sub-Zaps in Zapier
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
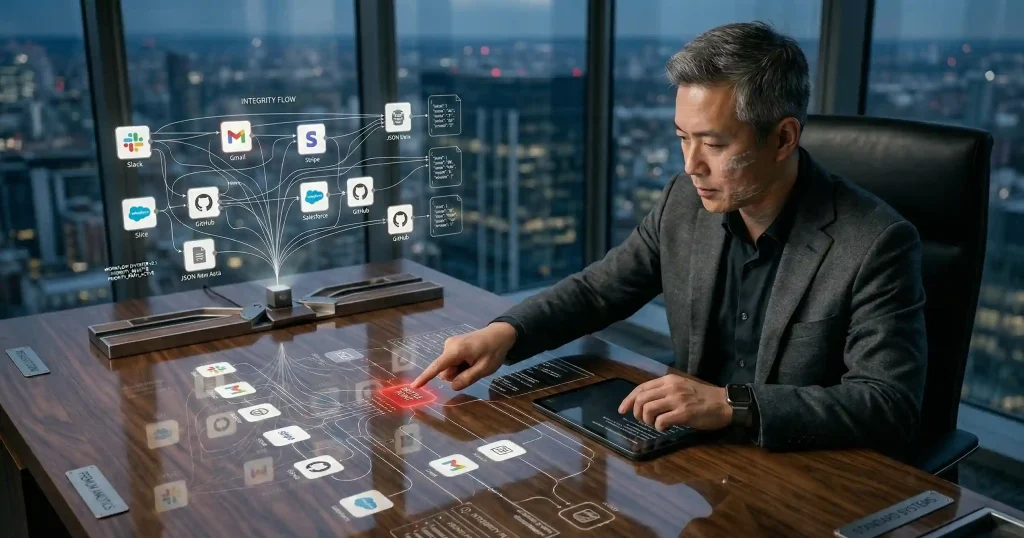
Beyond the No-Code Ceiling: Why n8n is the Engine for High-Complexity Enterprise Automation
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
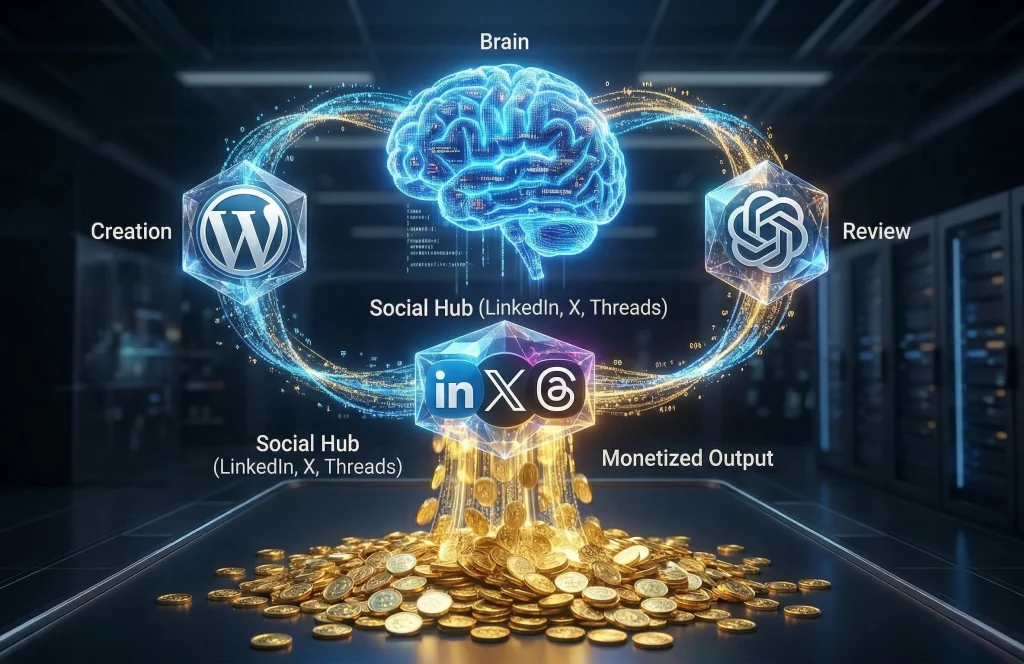
Automate Your Marketing Stack: From Content Creation to Social Distribution
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
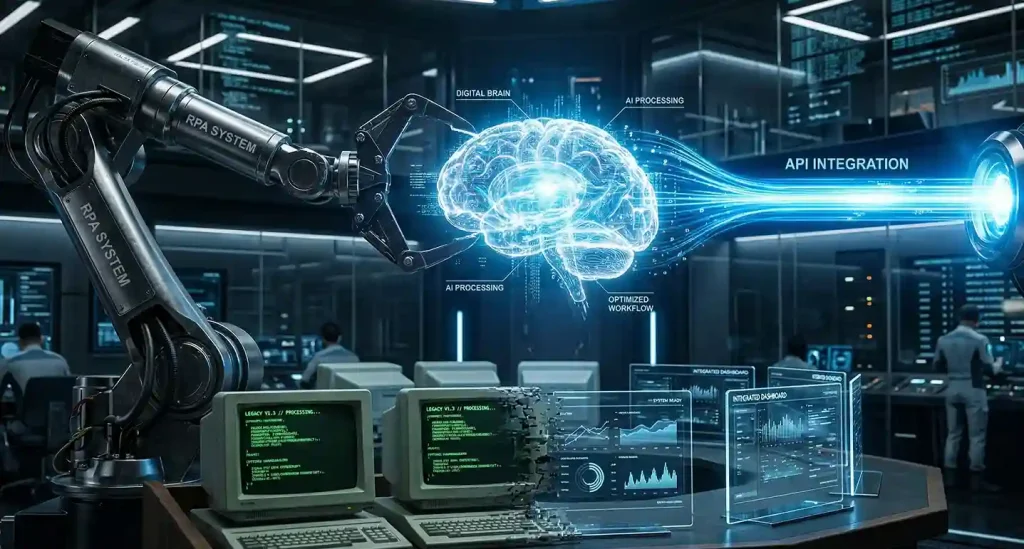
RPA vs. API Automation: When to Use Bots vs. Direct Integrations
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
Your Data, Your Rules: Why 2026 is the Year of Self-Hosted n8n
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
Beyond Simple Triggers: Building Self-Thinking AI Agents in n8n
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
Stop Overpaying: Why n8n is the “Zapier-Killer” of 2026
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.
The Invisible Concierge: How Agentic AI is Redefining Travel in 2026
Are you pasting sensitive data into public AI tools? Learn the massive security and compliance risks of “Shadow AI” and how to protect your data.